Ransomware is no petty crime — security experts estimate that cyber criminals collected at least $1 billion from victims globally in 2016. While law enforcement agencies are often called to investigate cyber crimes from ransomware, they haven’t escaped becoming victims themselves. In fact, 18% of the ransomware attacks reported in 2016 targeted a public sector agency. In early 2018, a simple email attachment tricked Licking County government employees into downloading a worm that crippled their entire network, including the 911 center, for 16 days.
How Do Agencies Find Themselves in This Position?
Ransomware is a threat that holds systems hostage by limiting end-user access to applications and information until certain financial demands are met. This crippling control is typically established by encrypting system applications so they cannot be accessed without the decryption keys. Victims are left with two unfortunate choices: either pay the ransom (often requested in cryptocurrency thus protecting the identity of the criminals), or refuse to pay and lose access to irreplaceable data.
Since ransomware attacks are typically aimed at widespread targets, the virus and the attack-chain (the sequence of steps that cyber criminals take to execute the attack) is often not sophisticated. Ransomware is inherently dependent upon the employees to open the door for cyber criminals to exploit technological vulnerabilities, as the attacks begin with social engineering ploys that are often executed through phishing emails. However, once executed, it may cost less to pay the ransom and (hope to) regain regular system operations than to crack the screen-lock or restore archived copies of the compromised data, as some healthcare institutions in Kansas and Los Angeles found out the hard way.
What Preventative Actions Can Agencies Take Today?
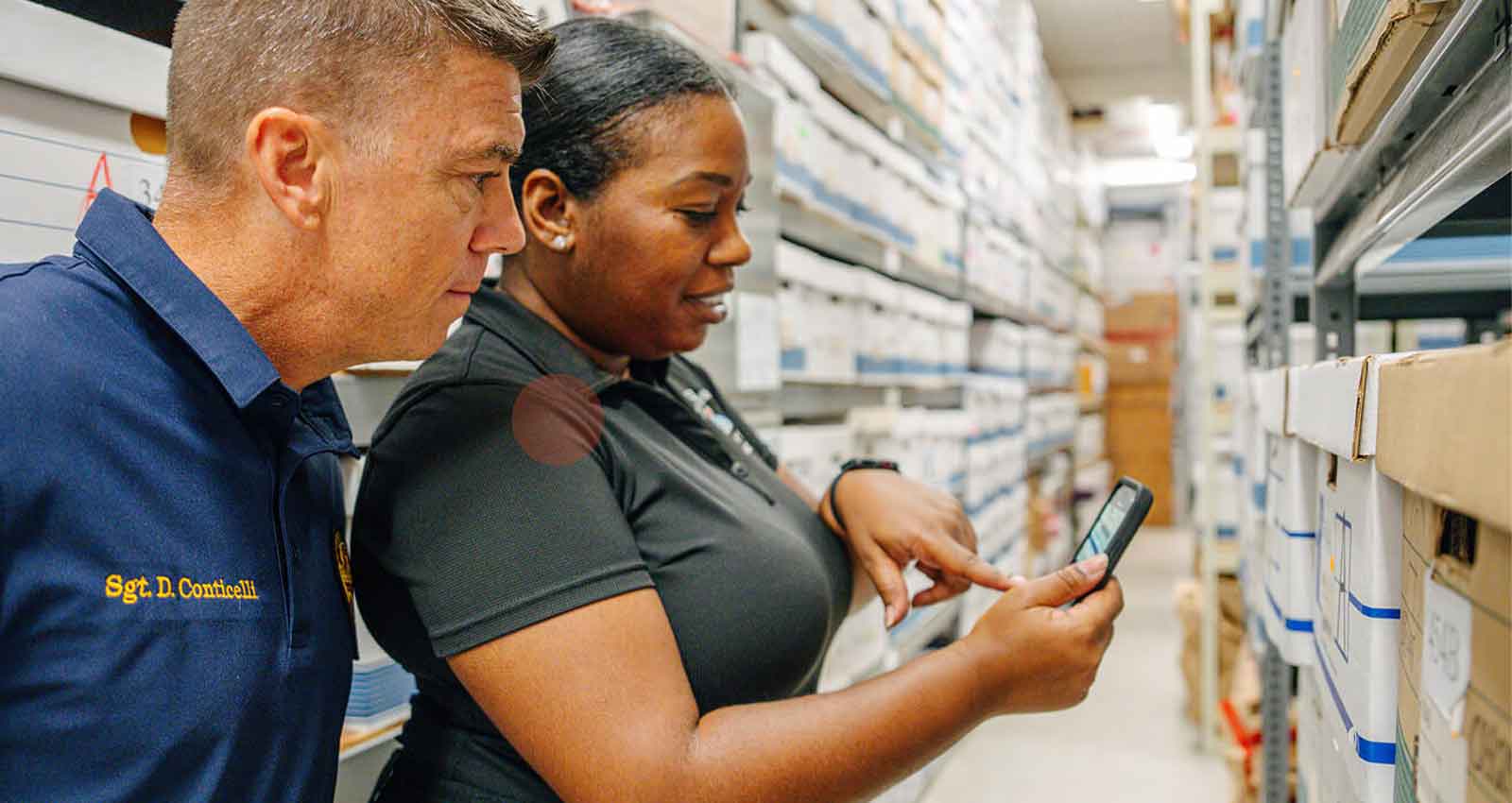
Cybercriminals are consistently evolving their attack methods and exploiting unforeseen vulnerabilities, making prevention a tough task in a technology-enabled society. Government agencies will be the most successful in combating the threat of ransomware by implementing a proactive and strategic approach to cybersecurity. Any approach lies with the IT employees and agency software systems that access, leverage, and secure records and data management services. Here are five cybersecurity measures to consider adopting today:
- Assess Data Backup Strategies
The most important preventative measure that your agency can invest in is your data backups. Data backups are the most secure when stored in secure cloud environments instead of vulnerable desktop machines or on-site servers. Agencies should also implement disaster recovery systems with layers of redundancy options; best-case in a secure cloud environment across multiple geographic locations, differing seismic plates, and flood zones. Backup data should also be classified based on its sensitivity and importance. - Cultivate Security Awareness Internally
The best protection an agency has against phishing emails, besides training their officers and administrators to circumvent illegitimate communications, is to install a powerful firewall with VPN technology and data encryption to all department computers. - Manage Physical Endpoint Security Vulnerabilities
Protecting and securing the entire Internet of Things (IoT) environment within an agency, including the data at rest and in transit is critically important. A secure cloud environment will include controls and several options for data encryption for all the phases of data activity. As a part of a robust and mature vulnerability management program, agencies can remove vulnerabilities as soon as they are discovered by automating firmware to push regular manual updates to connected devices such as city security and traffic cameras. In addition, agencies should implement physical deterrence to discourage physical tampering or wiring of third-party man-in-the-middle devices. - Enable Advanced Threat Intelligence and Proactive Risk Mitigation
Restricting sources of inbound and outbound network traffic and committing to consistent monitoring of network traffic is the best way to be proactive when it comes to risk mitigation. Whether in a secure cloud or on-premise, agencies should implement policy-driven security measures that address risks across connected devices, distributed data sources, and their increasingly mobile workforce. - Executing Audits and Testing
Growing cybersecurity risks, new vulnerabilities, and unforeseen workforce behavior may facilitate ransomware attacks. Internal audits and testing ensure agencies are prepared as the threat evolves. Secure cloud providers, like Amazon Web Services, outline specific and regular intervals in their security audit guidelines. Since these efforts potentially cause significant changes across the people, processes, technologies, and strategies that define the organization and its operations, it is important to ensure stakeholder buy-in before making these decisions.
Ransomware can — and has — crippled mission-critical government technology and jeopardized agencies’ ability to respond to emergencies and protect sensitive community data. This is a risk that cannot be ignored. Ransomware threat mitigation should be a regular part of any cybersecurity strategy. Ultimately, adequate preparation and proactive defense mechanisms will help government agencies render the ransomware business model obsolete.
Kevin Fray is the Lead Solutions Architect at Mark43, where he consults public safety agencies on their transition to cloud-based CAD and RMS systems. Learn more about how public safety agencies can take advantage of the security benefits of the cloud here.